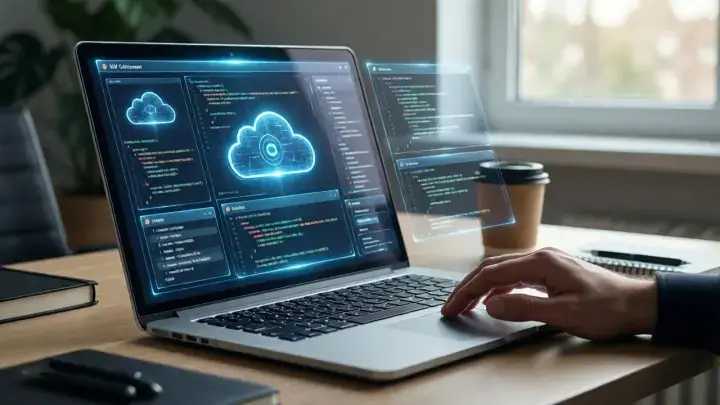
Protecting Sensitive Data Across Multiple Cloud Providers
The Challenge of Multicloud Data Security
Organizations today often use several cloud providers to meet their business needs. This multicloud approach offers flexibility and cost savings, but it also introduces new risks for sensitive data. Each cloud provider has its own security features, policies, and management tools. As a result, protecting sensitive data across these different environments can be complex and requires careful planning.
Another challenge is the lack of standardization between cloud vendors. Security configurations and monitoring tools may work differently depending on the provider. This can lead to gaps in protection if not managed carefully. Organizations must understand the unique risks and responsibilities associated with each cloud platform, as well as the shared responsibility model for cloud security.
Many businesses also face challenges in keeping track of where their sensitive data resides. As workloads move between public, private, and hybrid clouds, data visibility can decrease, making it harder to enforce security policies. This can create vulnerabilities if sensitive data is accidentally exposed or left unprotected.
Key Strategies for Data Protection
A strong security strategy should include access control, encryption, and continuous monitoring. Using cloud data protection solutions for hybrid and multicloud environments can help organizations manage risks by centralizing security policies and automating compliance checks. It’s also important to classify data based on its sensitivity and ensure that only authorized users have access to the most critical information.
Data classification helps organizations prioritize their security efforts. Not all data requires the same level of protection, so identifying the most sensitive data is key. Automated tools can help monitor where sensitive data is stored and who has access to it. Regular reviews of user permissions are recommended to prevent privilege creep.
In addition, organizations can look to external resources for up-to-date guidance. For instance, the Cloud Security Alliance provides a comprehensive set of best practices for cloud security, which can help organizations assess their cloud security posture.
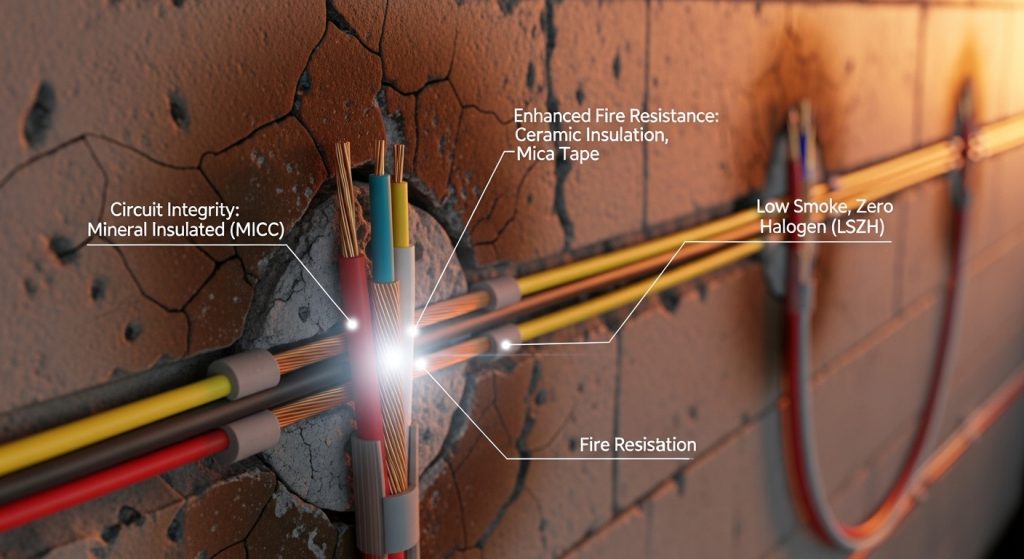
Encryption as a First Line of Defense
Encrypting data both at rest and in transit is essential when working with multiple cloud providers. Encryption scrambles data so that it can only be read by those with the proper decryption keys. This reduces the risk of unauthorized access, even if a breach occurs. For more information on encryption standards and best practices, visit the National Institute of Standards and Technology’s page on encryption guidelines.
Encryption should be applied not only to files and databases, but also to backups and archives. Organizations should use strong, industry-standard algorithms and manage their encryption keys securely. Key management is a critical aspect; losing control of encryption keys can result in data loss or unauthorized access.
Some cloud providers offer built-in encryption services, but organizations must ensure these services meet their security requirements. Using third-party encryption tools can provide an extra layer of protection, especially when dealing with highly sensitive information.
Centralizing Access Management
Managing user access across different cloud platforms is a major challenge. Identity and access management (IAM) tools help control who can view or modify sensitive data. These tools allow organizations to set strict permissions and monitor user activity. The Cybersecurity and Infrastructure Security Agency offers guidance on identity and access management to support secure cloud operations.
Single sign-on (SSO) solutions can simplify access across multiple cloud environments. SSO allows users to log in once and access all authorized resources, reducing the risk of weak or reused passwords. Multi-factor authentication (MFA) adds another layer of security by requiring a second form of verification, such as a code sent to a mobile device.
Organizations should regularly review and update user permissions, especially when employees change roles or leave the company. Monitoring for unusual access patterns can help detect potential insider threats or compromised accounts.
Ensuring Compliance and Meeting Regulations
Many industries have strict rules about how data must be stored and protected. Organizations need to comply with laws like GDPR, HIPAA, or PCI DSS, depending on their sector. Regular audits and assessments can help identify gaps in compliance. The U.S. Department of Health and Human Services provides resources on healthcare data security and compliance for those in the medical field.
Compliance is not just about avoiding fines; it also helps build trust with customers and partners. Organizations should document their security controls and keep records of all compliance activities. Automated compliance tools can track changes and alert administrators to potential violations.
It’s also important to stay up to date with changes in regulations. The European Union Agency for Cybersecurity (ENISA) regularly publishes updates and advice on data protection for organizations operating in the EU.
Continuous Monitoring and Incident Response
Monitoring tools can track suspicious activity across cloud environments in real time. If an incident occurs, having a clear response plan can limit damage and speed up recovery. Regular testing and updates to security protocols are necessary to address new threats as they emerge.
Incident response plans should include roles and responsibilities, communication procedures, and steps for containing and investigating incidents. Tabletop exercises and simulations can help teams practice their response and identify areas for improvement.
For further guidance on building effective incident response strategies, the U.S. Computer Emergency Readiness Team provides a useful resource on incident handling.
Training and Building a Security Culture
Technology alone cannot protect sensitive data. Employees must be trained on security best practices and understand their role in protecting information. Regular awareness training can help staff recognize phishing attempts, use strong passwords, and follow safe data handling procedures.
Building a security-focused culture involves leadership support and clear communication. Security policies should be accessible and easy to understand. Encouraging employees to report suspicious activity can help organizations respond to threats more quickly.
Ongoing training ensures that new risks and techniques are addressed as the threat landscape evolves. Organizations can turn to government agencies and educational institutions for free or low-cost training materials.
Backup and Disaster Recovery in Multicloud Environments
Having reliable backups is essential for protecting sensitive data in the cloud. Organizations should create regular backups and store them in separate, secure locations. Testing backup and recovery procedures helps ensure that data can be restored quickly in the event of a cyberattack or system failure.
A robust disaster recovery plan should account for the unique challenges of multicloud environments. This includes coordinating recovery efforts across different cloud providers and ensuring that backup data is encrypted and protected from unauthorized access.
Documenting recovery steps and assigning responsibilities in advance can help minimize downtime and data loss during an emergency.
Emerging Trends in Multicloud Data Protection
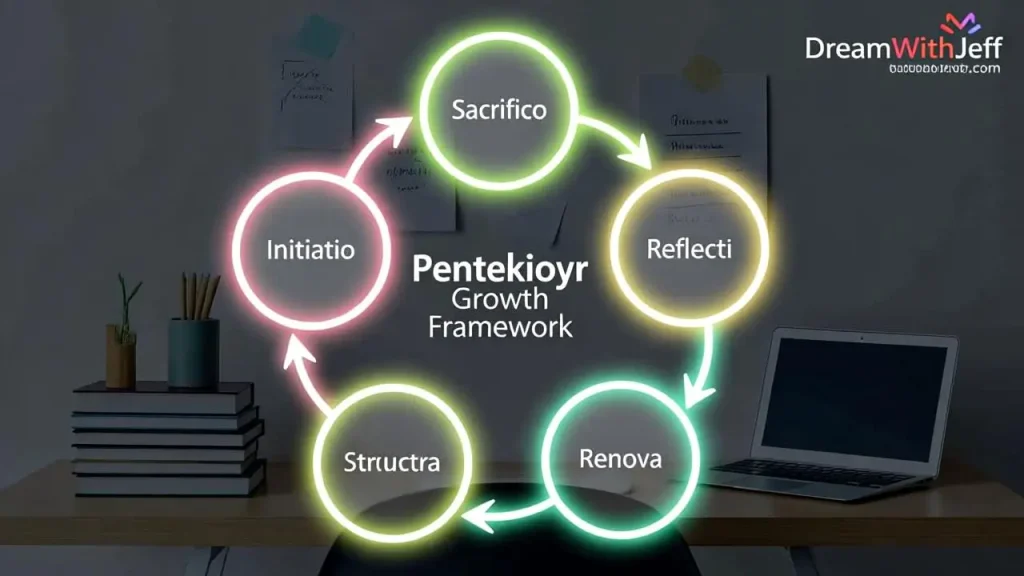
As technology evolves, new tools and techniques are emerging to help organizations protect data across multiple cloud providers. Zero trust security models, automated threat detection, and artificial intelligence are increasingly being used to strengthen cloud security.
Zero trust assumes that no user or device should be trusted by default, even if they are inside the network. This approach requires strict verification for every access request and continuous monitoring of user behavior.
Staying informed about the latest trends and adopting new solutions can help organizations stay ahead of cyber threats and improve their overall security posture.
Conclusion
Protecting sensitive data across multiple cloud providers is a complex but vital task. By combining strong encryption, centralized access management, and continuous monitoring, organizations can reduce risks and keep their data safe. Staying informed about regulations and following best practices will help ensure data security in any multicloud environment.
FAQ
What is multicloud data protection?
Multicloud data protection refers to securing sensitive information across multiple cloud platforms. It involves using consistent security policies, encryption, and access controls to prevent unauthorized access or data loss.
Why is encryption important for cloud data security?
Encryption protects data by making it unreadable to anyone without the correct key. This is important in the cloud because it reduces the risk of data breaches, even if someone gains unauthorized access.
How can organizations control access to sensitive data?
Organizations can use identity and access management tools to set permissions and monitor who can view or change sensitive data. This limits access to only those who need it for their work.
What regulations affect cloud data security?
Regulations like GDPR, HIPAA, and PCI DSS require organizations to protect sensitive data and report breaches. Compliance helps avoid fines and maintain customer trust.
What should a cloud incident response plan include?
A cloud incident response plan should outline steps for detecting, containing, and recovering from security incidents. It should also include communication procedures and regular testing.
For More Visits: Mymagazine

 English
English 

















































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































![swimsuit edition [abbb] - 1.20 21 swimsuit edition - chapter](https://mymagazine.blog/wp-content/uploads/2025/09/swimsuit-edition-abbb-1.20-21-swimsuit-edition-chapter1-1024x574.webp)























































































































































































































































